Security Audit of a 1C-Bitrix Site
A security audit is not a one-tool scan. It is a systematic review of platform configuration, server settings, code, and access rights. The deliverable is not just a list of vulnerabilities — it is a prioritized remediation plan with risk assessment.
What Is Checked First
Core and module versions — Marketplace → Updates. An outdated core is a source of known CVEs. Check changelogs for security patches. Critical updates are released outside the regular schedule.
File and directory permissions — a common problem on shared hosting:
find /var/www/html -type f -name "*.php" -perm -o+w
find /var/www/html/upload -type f -name "*.php"
PHP files in /upload/ are a clear sign of infection or incorrect permissions.
Open directories — /.git/, /bitrix/backup/, /bitrix/php_interface/ must not be accessible from outside. Verify using curl or a browser.
Code and Component Review
Custom components in /local/components/ and /local/templates/ are the primary attack vector. Check for:
- Output escaping:
htmlspecialchars(),\Bitrix\Main\Text\HtmlFilter::encode() - SQL queries: only via
$DB->Query()with escaping, or through the D7 ORM - File uploads: MIME type validation via
\CFile::CheckImageFile(), extension restrictions - Use of
$_REQUEST,$_GET,$_POSTwithout validation
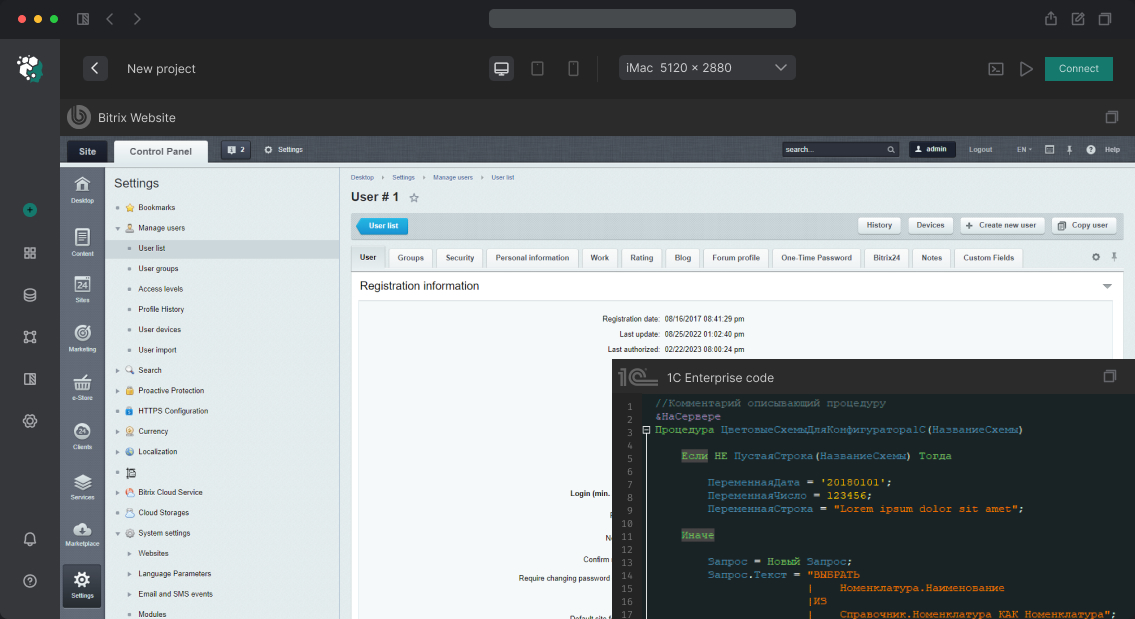
Built-in Bitrix scanner: Security → Security Scanner. Checks for known infection patterns in files. Does not replace a manual audit, but quickly identifies common injections.
Server Configuration Review
-
display_errors = Offin PHP on production -
expose_php = Off— do not expose the PHP version in response headers - Security headers:
X-Content-Type-Options,X-Frame-Options,Content-Security-Policy - Open ports beyond 80/443 — check with
nmapor via the hosting control panel
Real-World Case
A security audit of an online store following a suspected infection. The Bitrix scanner found nothing. A manual check using find /var/www -name "*.php" -newer /var/www/html/bitrix/modules/main/classes/general/module.php revealed 12 files with modified timestamps — inside /upload/resize_cache/. All contained obfuscated PHP code with base64 encoding. The attack vector: a vulnerability in an outdated custom image upload component with no extension validation.
Audit Deliverable
The output is a report categorized by severity level: critical (requires immediate action), high (within one week), medium, and low. Each item includes a specific technical remediation recommendation.
Delivery Time
Basic security audit — 1 to 2 business days. In-depth audit including custom module code analysis — 3 to 5 days.