Two-Factor Authentication Setup in 1C-Bitrix
Two-factor authentication (2FA) is natively supported in Bitrix via OTP (one-time passwords) using the TOTP standard — compatible with Google Authenticator, Authy, and Microsoft Authenticator. Setup takes less than an hour but is critically important for administrator accounts.
Built-in OTP Authentication
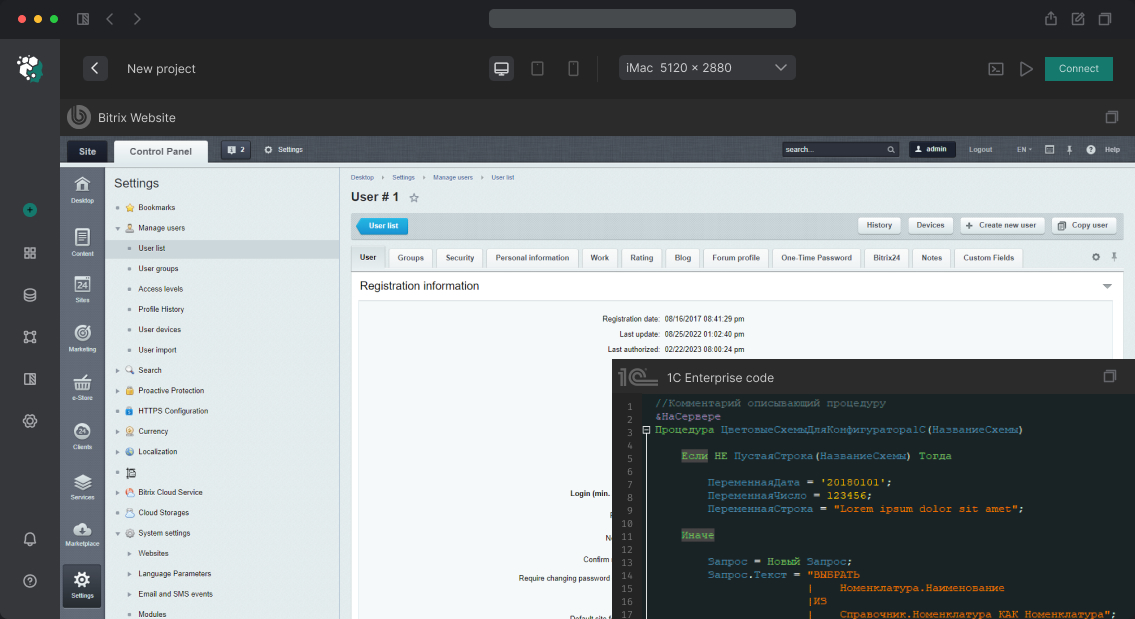
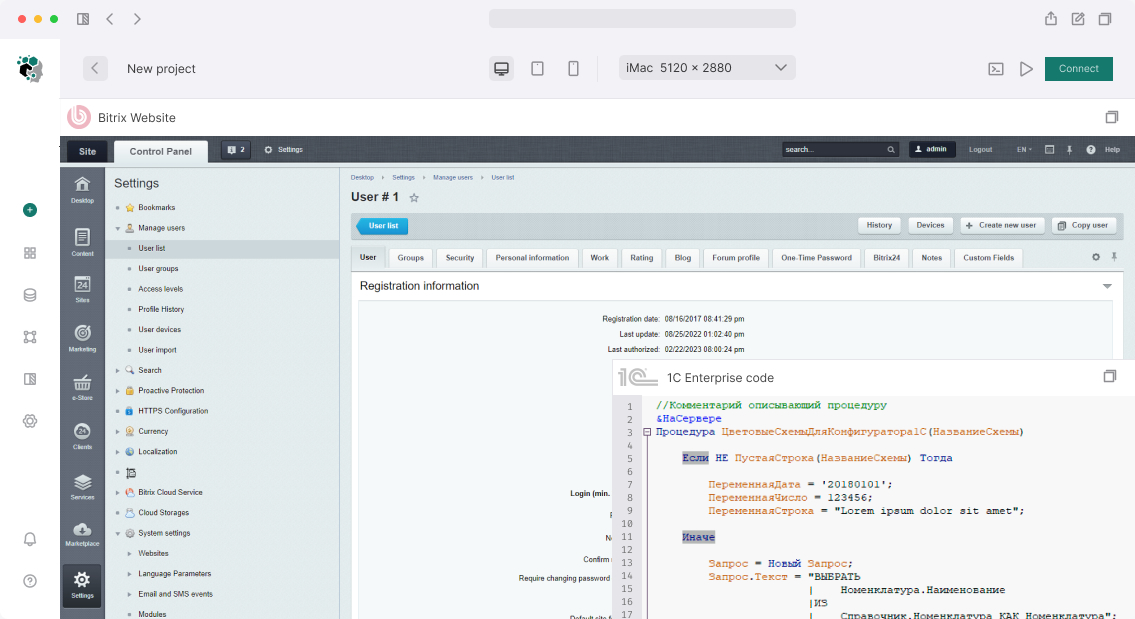
The 2FA module is part of the main module. Enable it under Settings → Main Module → Two-Factor Authorization.
Parameters:
- Mandatory use — for selected user groups. Always enable it for the "Administrators" group
- Code validity period — TOTP standard: 30 seconds. Do not change unless necessary
- Code length — 6 or 8 digits
Once enabled, the user is shown a QR code on their next login to set up an authenticator app. The secret is stored in b_user.OTP_SECRET in encrypted form.
Configuration for Specific Groups
If you need to apply 2FA only to certain users (e.g., staff but not customers):
-
Settings → User Groups → [target group] → Two-Factor Authorization: Required - Or programmatically via the
OnAfterUserAuthorizeevent — check the group and redirect to the OTP setup page
SMS Authentication
Bitrix does not have a built-in SMS gateway for 2FA, but this can be addressed through the OnOTPCheck event handler — any SMS provider can be integrated (e.g., SMS.ru, SMSC.ru). Implementation: on first login, a code is generated, sent via SMS, and entered by the user.
Alternatively, use Marketplace modules for SMS 2FA if you prefer not to write a custom handler.
Real-World Case
An online store had an administrator account compromised through brute-force (the password Admin2023 did not fall under the minimum length restrictions of an older policy). The attacker modified payment requisites in the checkout settings. Post-incident response: mandatory 2FA for the "Administrators" and "Managers" groups, and an audit of all existing passwords via b_user.PASSWORD to identify weak hashes (MD5 without salt — legacy accounts).
Backup Codes
The built-in OTP does not generate backup codes automatically — this needs to be implemented separately, or a 2FA reset procedure via an administrator must be documented. Without access to the phone and without backup codes, a user permanently loses access to their account.
Delivery Time
Enabling and configuring built-in OTP for all groups — 2–3 hours. With custom SMS integration — 1 business day.